The number that once made quantum encryption-breaking seem like a distant, almost theoretical threat has just been slashed by a factor of more than 100. New research suggests that a quantum computer armed with as few as 10,000 qubits — not the millions previously assumed — could be enough to crack the encryption algorithms protecting the world’s most sensitive data.
That shift in understanding is not a minor technical footnote. It moves the timeline for a real-world cryptographic threat from something that felt safely far away to something that demands urgent attention right now.
The key is not raw computing power. It is a smarter approach to error correction — and it changes almost everything about how we should be thinking about quantum security.
Why Quantum Computers and Encryption Are on a Collision Course
Modern encryption — the kind that secures your bank account, your private messages, and classified government communications — relies on mathematical problems that would take a classical computer an impractical amount of time to solve. Quantum computers, in theory, can tackle those same problems exponentially faster.
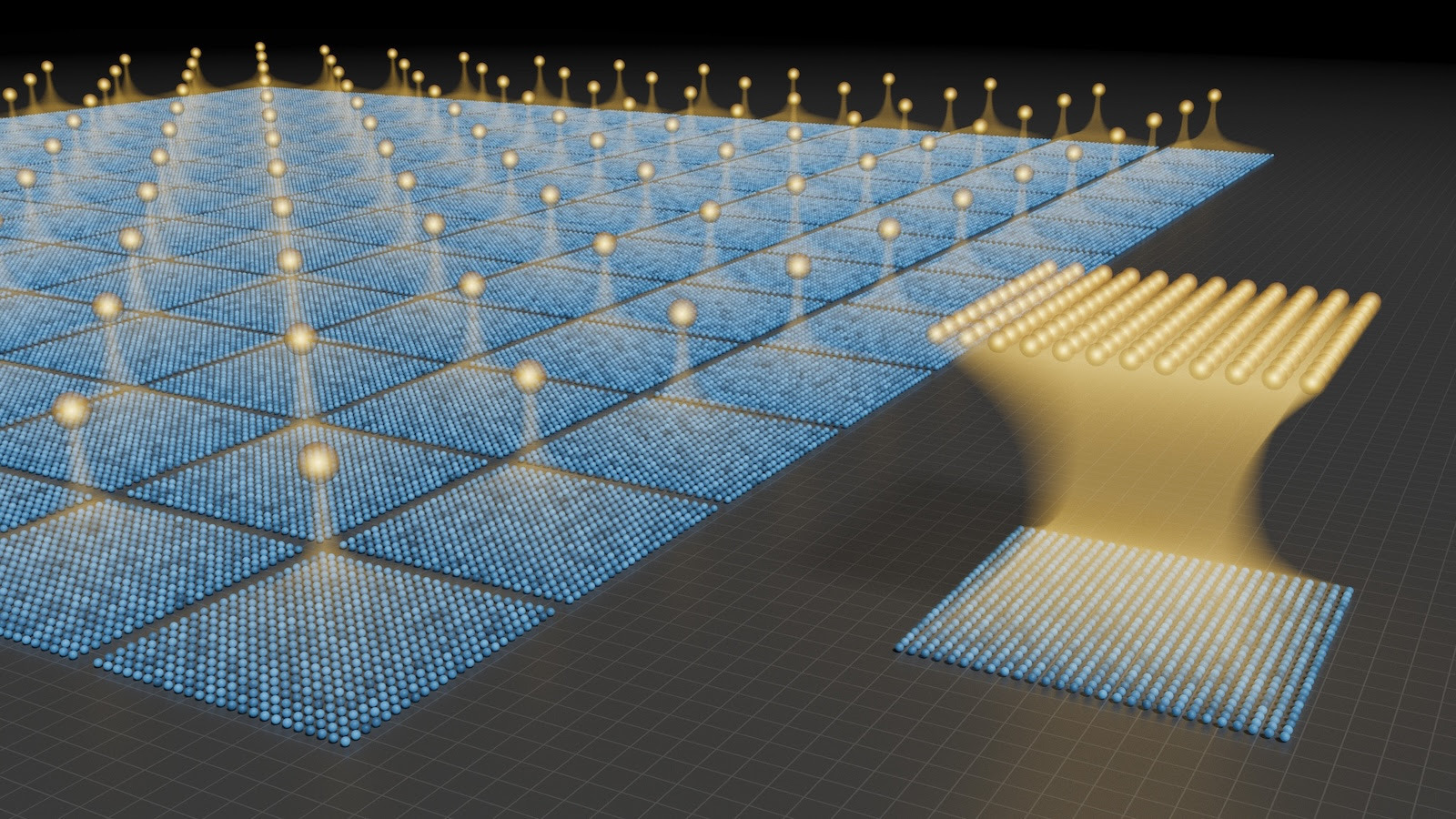
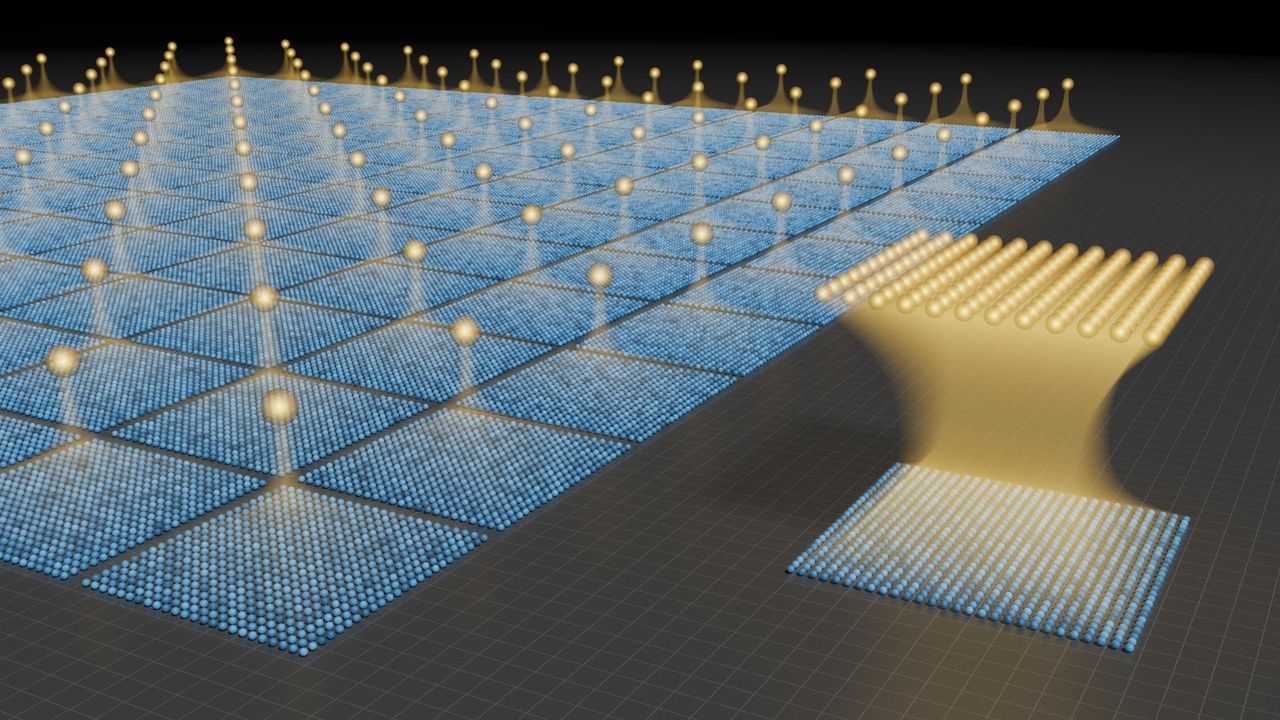
The catch has always been error rates. Quantum bits, or qubits, are extraordinarily fragile. They are prone to interference from heat, vibration, and electromagnetic noise — a phenomenon known as decoherence. To compensate, researchers have relied on error-correction schemes that bundle hundreds of physical qubits together to represent a single reliable “logical” qubit.
That overhead is enormous. If you need thousands of logical qubits to break an encryption algorithm, and each logical qubit requires hundreds of physical qubits to stay stable, you are suddenly talking about millions of physical qubits total. That scale has kept encryption-breaking quantum computers firmly in the realm of science fiction — until now.
The Breakthrough That Rewrites the Math
The new research, highlighted by scientists and covered by Live Science, centers on a dramatically more efficient error-correction scheme. Where previous approaches required hundreds of physical qubits per logical qubit, this new method reduces that overhead by more than 100-fold.
The practical consequence is staggering. Instead of needing millions of physical qubits to achieve the logical qubit count necessary to break widely used cryptographic systems, a quantum computer may only need around 10,000 physical qubits to do the job.
That is not a number that exists only in a laboratory fantasy. Several quantum computing programs around the world are already operating at or approaching qubit counts in the thousands. The gap between current hardware and encryption-breaking capability just got a lot narrower.
What This Means for the Encryption Keeping Your Data Safe
The encryption algorithms at risk are not obscure or legacy systems. They are the widely used cryptographic standards that underpin global digital security — the kind baked into browsers, financial systems, government communications, and corporate infrastructure worldwide.
Researchers have warned for years that a sufficiently powerful quantum computer could render these systems obsolete. The debate has always been about timing. This new finding shifts that debate considerably.
| Factor | Previous Assumption | New Research Suggests |
|---|---|---|
| Physical qubits needed to break encryption | Millions | ~10,000 |
| Physical qubits per logical qubit (error correction) | Hundreds | Reduced by more than 100-fold |
| Threat timeline perception | Distant / theoretical | Significantly closer |
The implication is clear: the window for transitioning to quantum-resistant encryption is shorter than the security community had widely assumed.
Who Is Actually at Risk — and How Seriously
The immediate concern is not that someone will crack your email password tomorrow. Building a stable, functional quantum computer with 10,000 well-behaved qubits is still an enormous engineering challenge. But the threat landscape has shifted in ways that matter to specific, high-stakes actors.
- Governments and intelligence agencies that rely on encrypted communications for national security have the most urgent exposure.
- Financial institutions whose transaction security depends on cryptographic integrity face long-term structural risk.
- Technology companies building systems intended to remain secure for decades need to begin transitioning now.
- Anyone storing sensitive encrypted data today faces a “harvest now, decrypt later” risk — adversaries can collect encrypted data now and decode it once the hardware catches up.
That last point is particularly sobering. You do not need to wait for the threat to arrive before the damage begins. Data stolen today under the assumption it is safely encrypted could be exposed years from now when the quantum hardware finally exists to break it.
The Race to Build Quantum-Resistant Systems Is Already Underway
The good news is that the cryptography community has not been standing still. Efforts to develop and standardize post-quantum cryptography — encryption methods designed to resist quantum attacks — have been in motion for years. The challenge is the pace and scale of adoption.
Transitioning global digital infrastructure to new cryptographic standards is not a simple software update. It requires coordinated action across governments, industries, and technology platforms. The more compressed the threat timeline becomes, the more urgency that transition carries.
Researchers argue that findings like this one should be treated not as alarming headlines but as useful recalibrations — the kind that help policymakers and engineers understand how much time they actually have, rather than how much time they assumed they had.
The error-correction breakthrough described in this research is, in a sense, a warning shot. It demonstrates that the engineering obstacles between today’s quantum computers and tomorrow’s encryption-breaking machines may be falling faster than expected.
Frequently Asked Questions
How many qubits do quantum computers currently have?
Several leading quantum computing programs are already operating in the hundreds to low thousands of qubits, though qubit quality and stability vary significantly across systems.
What is the significance of reducing error-correction overhead by 100-fold?
Previous error-correction schemes required hundreds of physical qubits to maintain a single reliable logical qubit. The new approach dramatically reduces that requirement, meaning far fewer total qubits are needed to perform complex operations like breaking encryption.
Does this mean current encryption is already broken?
No. Building a stable quantum computer with 10,000 high-quality qubits remains a major engineering challenge, but the new research significantly narrows the gap between current hardware and the threshold needed to break widely used encryption algorithms.
What is post-quantum cryptography?
Post-quantum cryptography refers to encryption methods designed to be secure against attacks from both classical and quantum computers. Standardization efforts for these algorithms have been underway for several years.
What is the “harvest now, decrypt later” threat?
This refers to the risk that adversaries collect encrypted data today — when it appears secure — and store it until quantum hardware capable of decrypting it becomes available in the future.
Should everyday users be worried right now?
The immediate risk to individual users is low, but organizations handling sensitive long-term data — governments, financial institutions, and large technology companies — face a more pressing need to begin transitioning to quantum-resistant encryption standards.




Leave a Reply